Our People
Get to know our teams and the stories of select staff members who share why they choose to work at Sands Capital.

News & Events
Read about some of the latest events, partnerships, and business highlights from Sands Capital.

Careers
Sands Capital portfolio managers reflect on five powerful lessons they have learned while investing through past downturns.
As artificial intelligence (AI) becomes a part of our everyday lives, making sure it’s transparent and unbiased has become a high priority for businesses, governments, and ordinary people. In this episode of What Matters Most, Scott Frederick, a Sands Capital managing partner, explains how software startup Credo AI is helping to keep AI models responsible. Join us as we look at how Credo AI aims to lead the way in this vital new field.
At Sands Capital we encourage our investment team to think in decades not quarters. Director of Research Michael Raab, CFA discusses how culture can support the visionary research needed to find businesses creating the future.
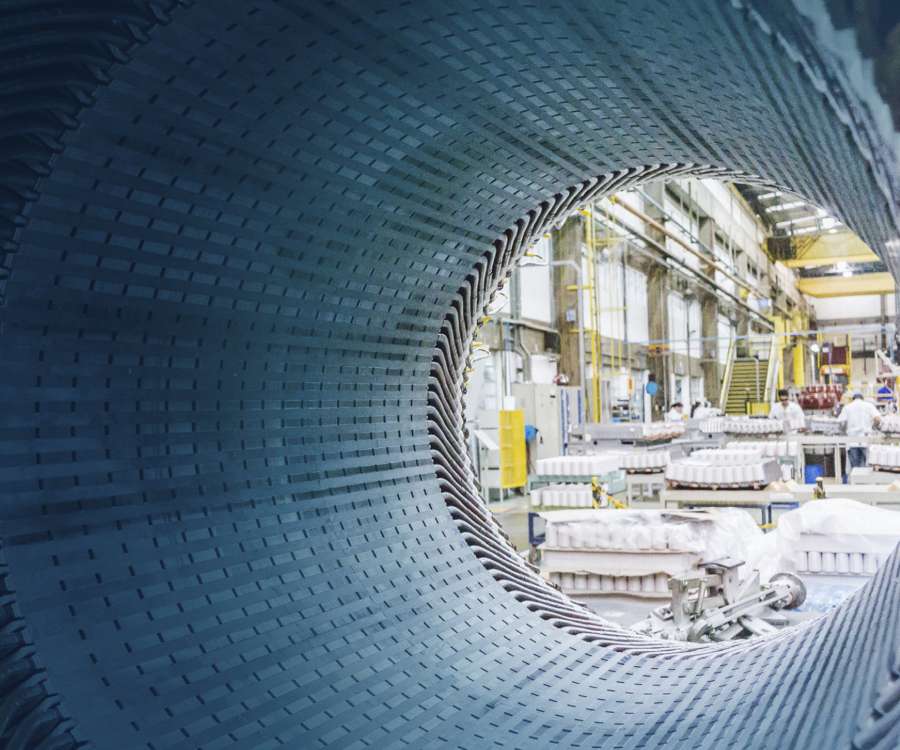
WEG is setting new standards for sustainability and innovation by focusing on energy efficiency and renewable solutions that deliver cutting-edge technologies to align with the needs of a rapidly changing world.

Philosophy & Approach
Our philosophy is rooted in the belief that, over time, stock prices will reflect the earnings power and growth of the underlying businesses.
Our latest annual report offers a comprehensive view of how we add value through active stewardship.

Public Equity
Our newest strategy takes an unconstrained approach to seeking the best growth businesses outside of the U.S.

Venture and Growth Equity
Sands Capital invests in innovative businesses across all stages of the growth spectrum